Recently, one of our clients approached us with a request to configure Single Sign-On (SSO) for Dialpad using Microsoft Entra ID. They had been using Microsoft Teams PSTN for communication, but due to cost considerations and additional features, they decided to switch to Dialpad.
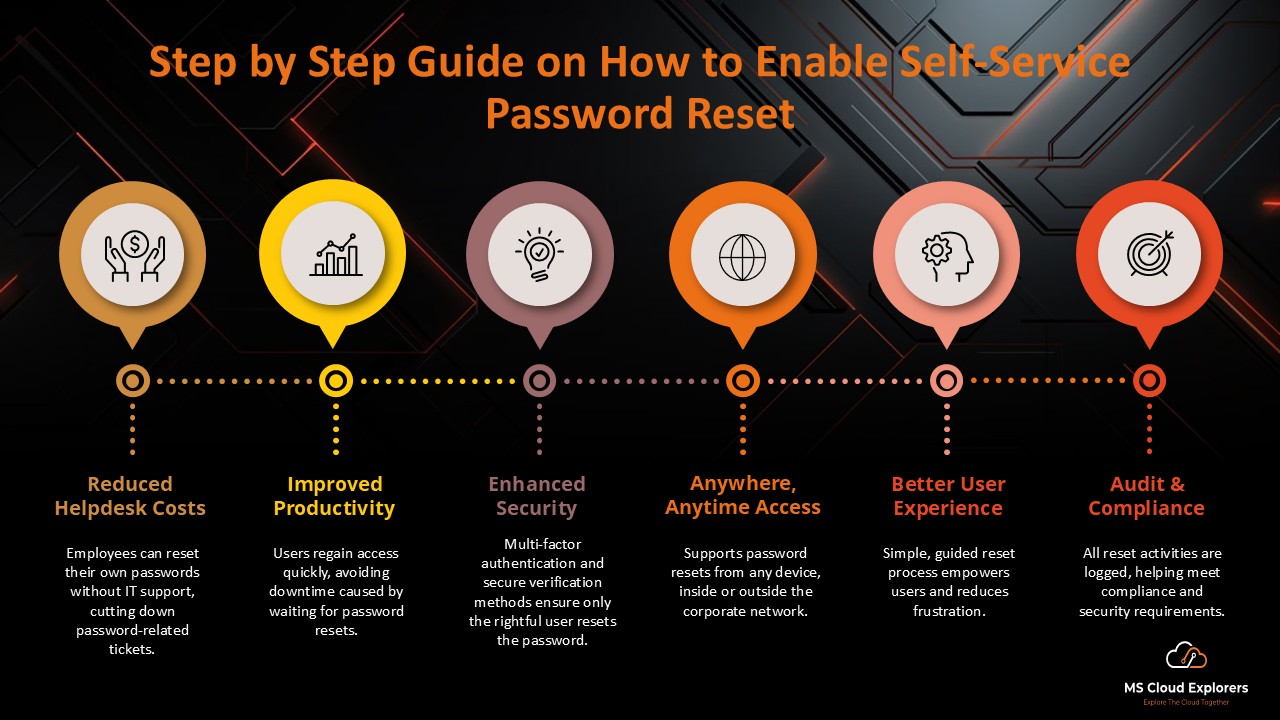
After the transition, they started facing a common issue — users frequently forgot their Dialpad passwords, leading to repeated login issues and an increase in password reset requests.
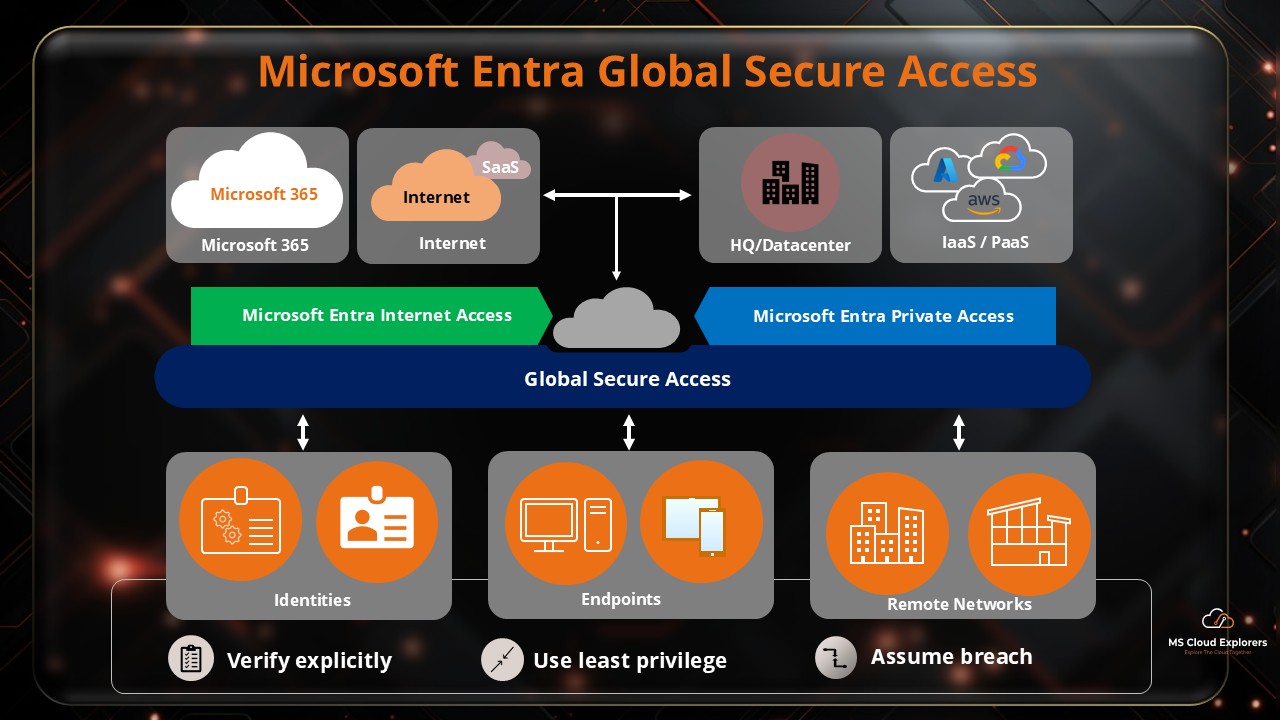
To solve this, we recommended implementing Single Sign-On (SSO) using Microsoft Entra ID. With SSO, users can log in to Dialpad using their existing organizational credentials, eliminating the need to manage multiple passwords while improving both security and user experience.
In simple terms, SSO allows seamless access to third-party applications like Dialpad by integrating them with your identity provider. However, setting it up requires proper configuration between Microsoft Entra ID and the application.
In this guide, I’ll walk you through the complete step-by-step process to configure Dialpad SSO with Microsoft Entra ID, based on a real-world implementation. If you’re planning to enable SSO for your organization, this guide will help you set it up quickly and correctly.
You can also deploy and Manage Dialpad app with the Microsoft Intune, check out the complete guide on how to package and deploy with Intune.
Why SSO with Dialpad and Microsoft Entra ID is Essential
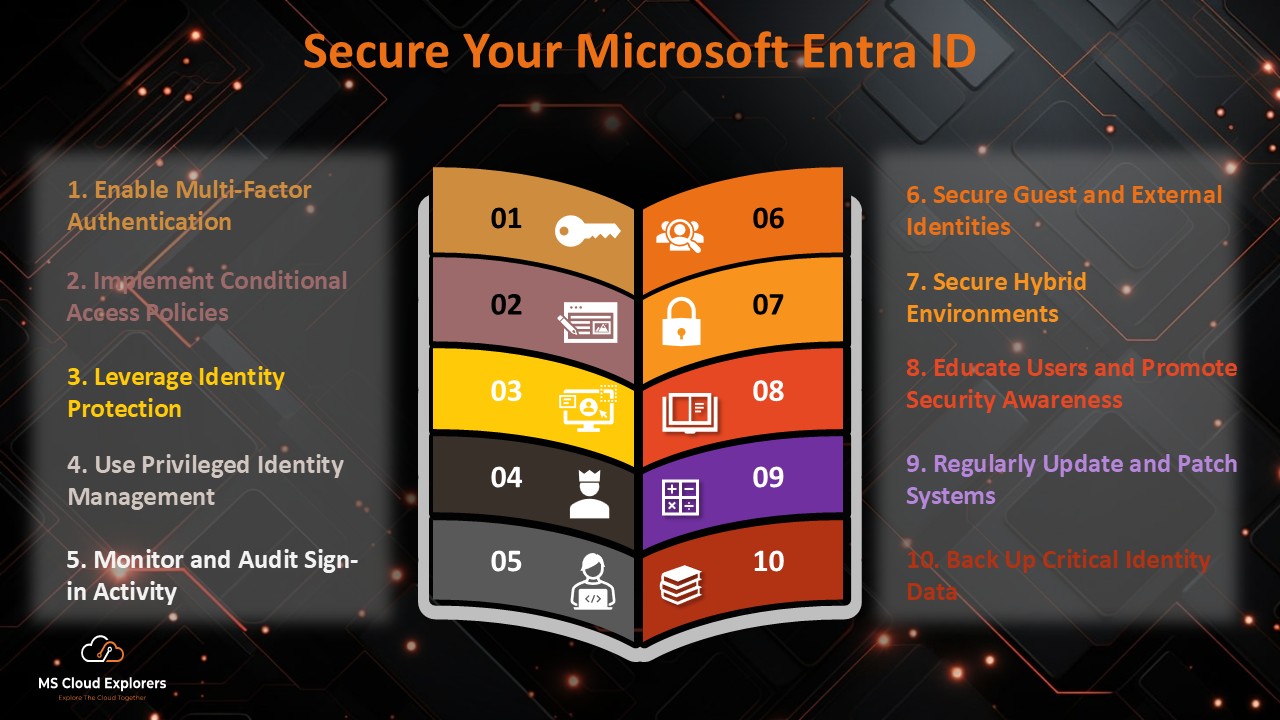
- Enhanced Security: SSO ensures that access to Dialpad is managed through Microsoft Entra ID, which offers robust identity protection mechanisms.
- Streamlined User Experience: Employees only need one set of credentials to access multiple applications, reducing login friction.
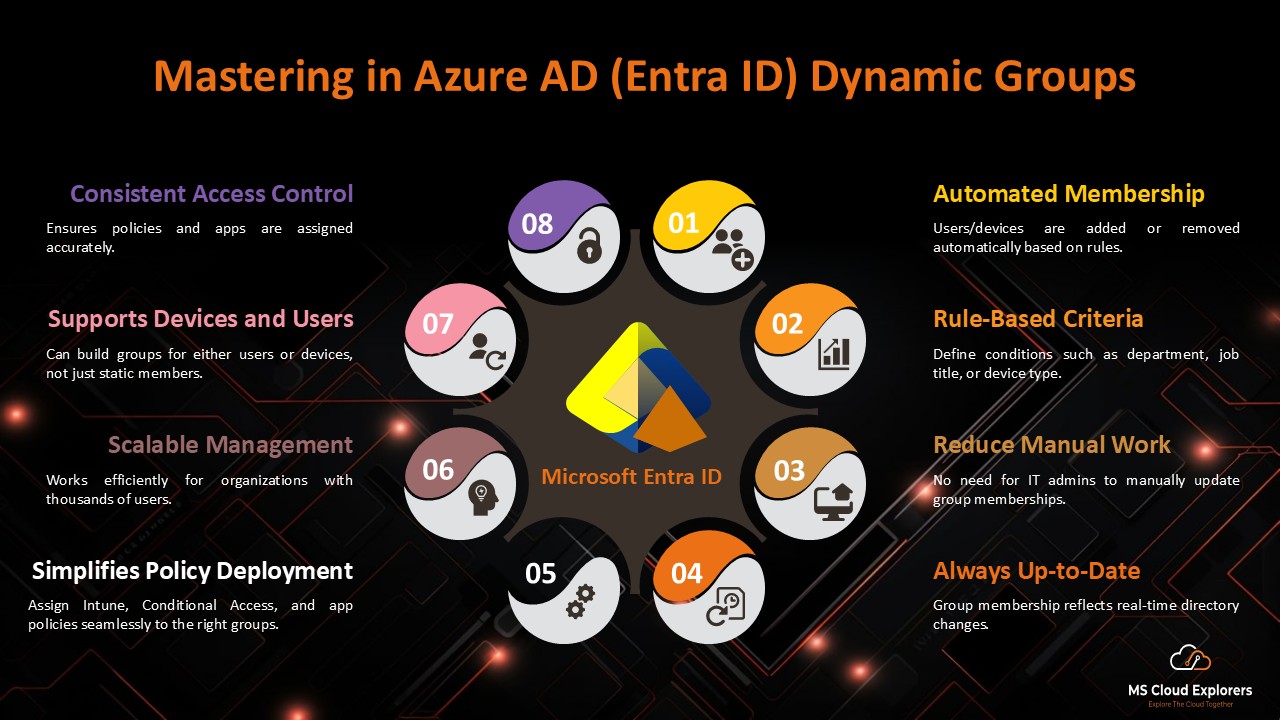
- Centralized Access Control: Administrators can manage access to Dialpad directly from Microsoft Entra ID, simplifying user provisioning and deprovisioning.
- Compliance: SSO enables organizations to enforce strict compliance policies, ensuring data security and regulatory adherence.
Benefits of Enabling SSO with Dialpad Using Microsoft Entra ID
- Time Savings: Users log in once with their Microsoft Entra ID credentials and access Dialpad instantly—no need to remember multiple passwords.
- Reduced IT Overhead: Fewer password reset requests mean less load on IT teams and more time for important tasks.
- Improved Security Posture: Centralized authentication helps prevent unauthorized access and reduces risks like phishing and weak passwords.
- Scalability: As your organization grows, managing user access becomes simple with centralized control from one place.
Steps to Configure Single Sign-on (SSO) for Dialpad with Microsoft Entra ID
Prerequisites
Ensure you have the following:
- An active Microsoft Entra ID subscription.
- Administrative access to the Microsoft Entra ID portal.
- A Dialpad admin account with access to the Admin portal.
- A premium subscription plan in Dialpad that supports SSO.
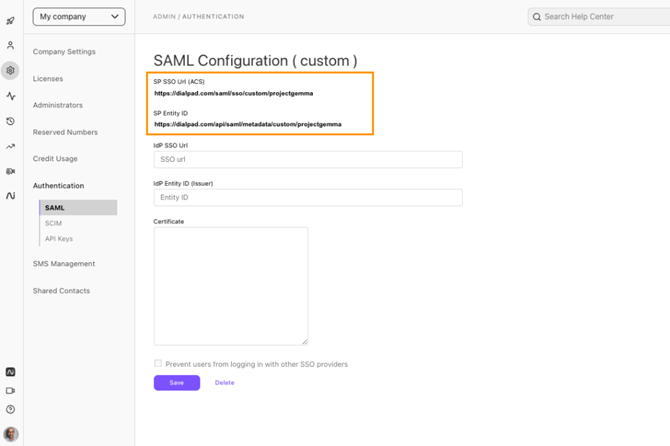
Step 1: Configure SSO in the Dialpad Admin Portal
- Log in to the Dialpad admin portal.
- Navigate to Settings > My Company > Authentication > SAML.
- Select “Custom” as the provider.
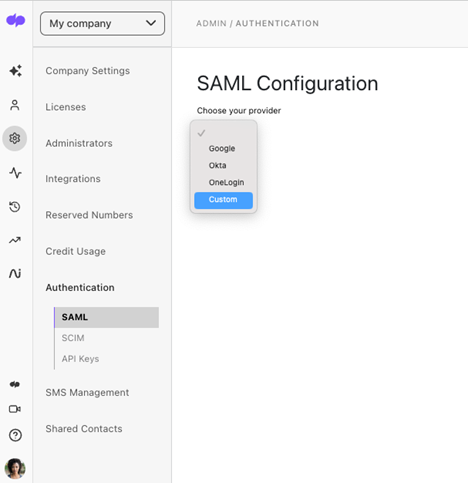
- Copy the SP SSO URL (ACS) and SP Entity ID for later use.
Step 2: Set Up the Application in Microsoft Entra ID
- Log in to the Microsoft Entra ID portal with administrator credentials.
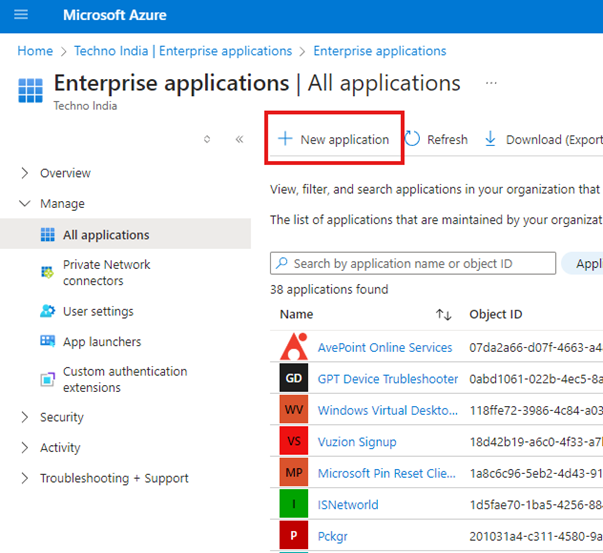
- In the left Side select the Enterprise Applications, under the Manage.
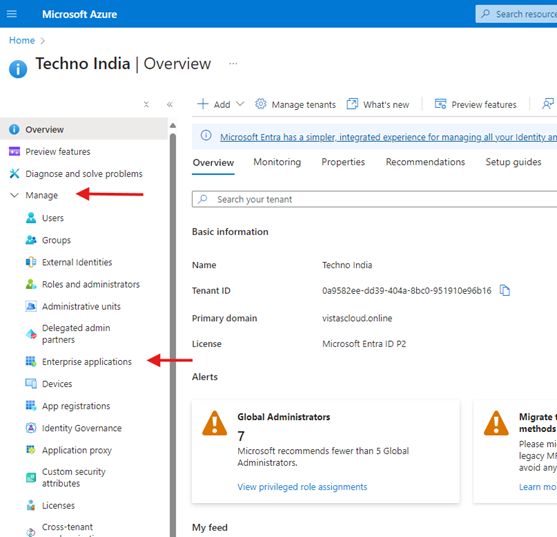
- Navigate to Enterprise Applications > New Application.
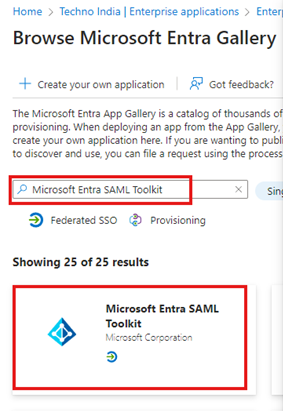
- In the Search type “Microsoft Entra SAML Toolkit” and click add it.
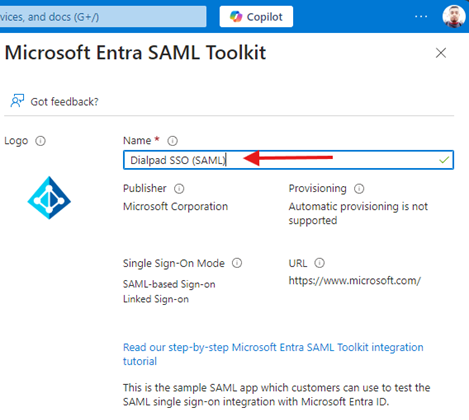
- Name the application “Dialpad SSO (SAML)” and click Create.
Step 3: Configure SSO in Microsoft Entra ID
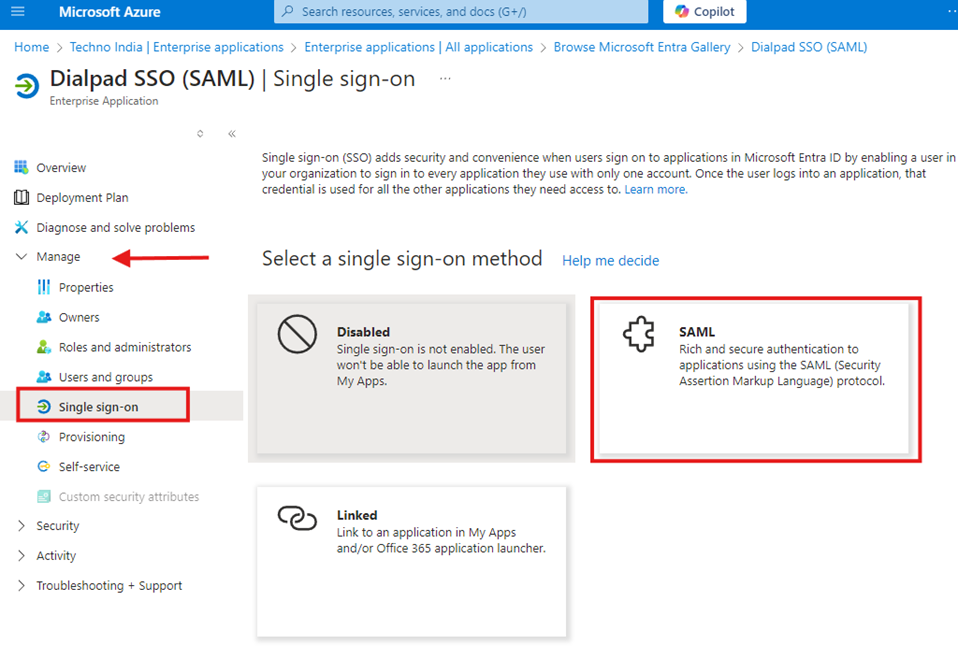
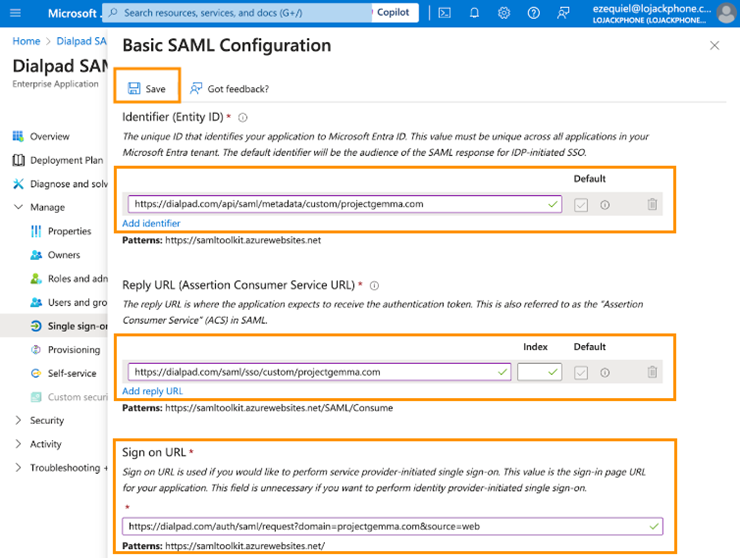
- Under the Dialpad app in Azure AD, navigate to Single Sign-On and select SAML.
- In the basic SAML configuration, enter the SP SSO URL and SP Entity ID copied earlier. Save the configuration.
- Add claims as required by Dialpad.
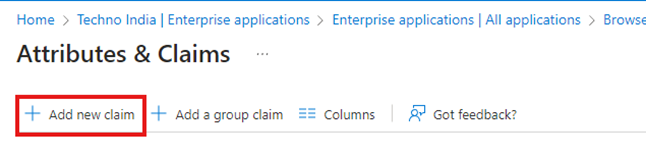
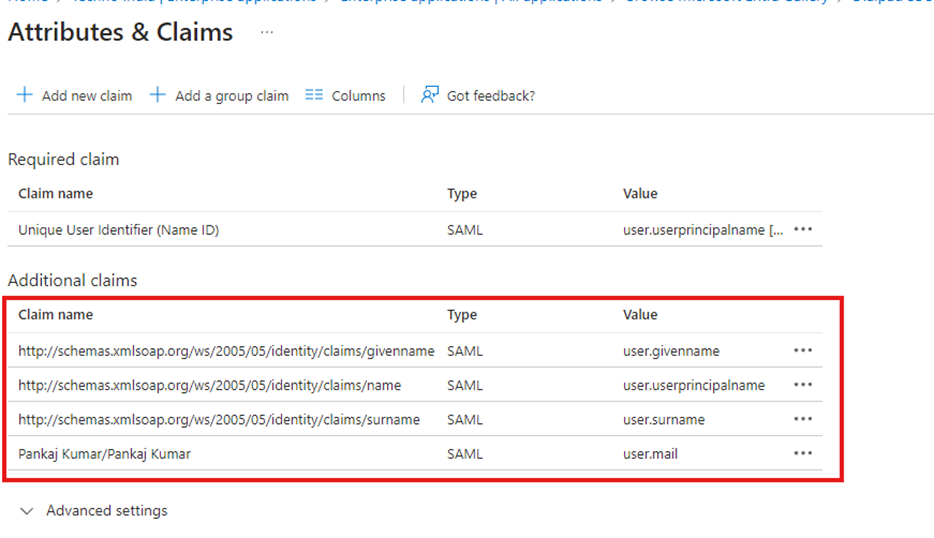
- Add the Name and Source Attribute as mentioned below
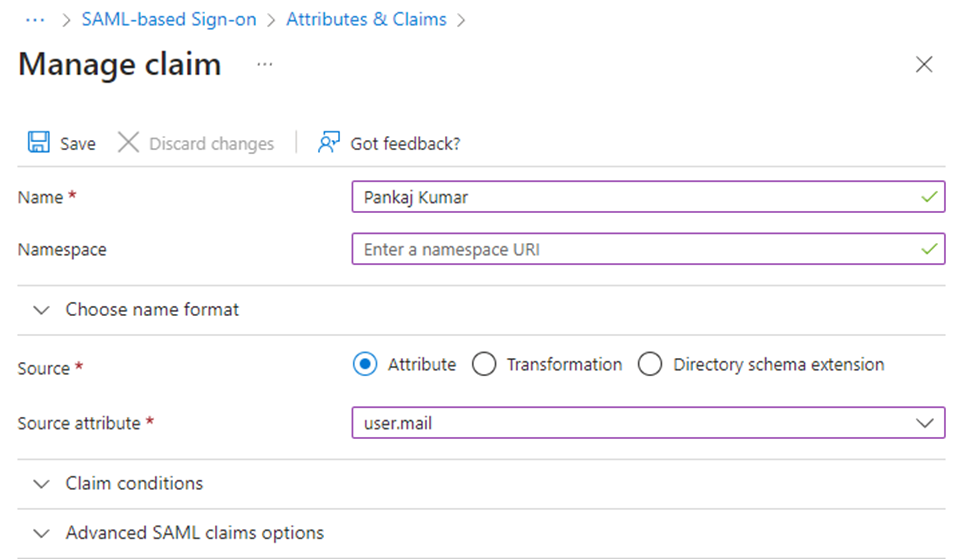
- Save the changes. Now you should see newly created claim.
- Download the certificate Under SAML Certificates.
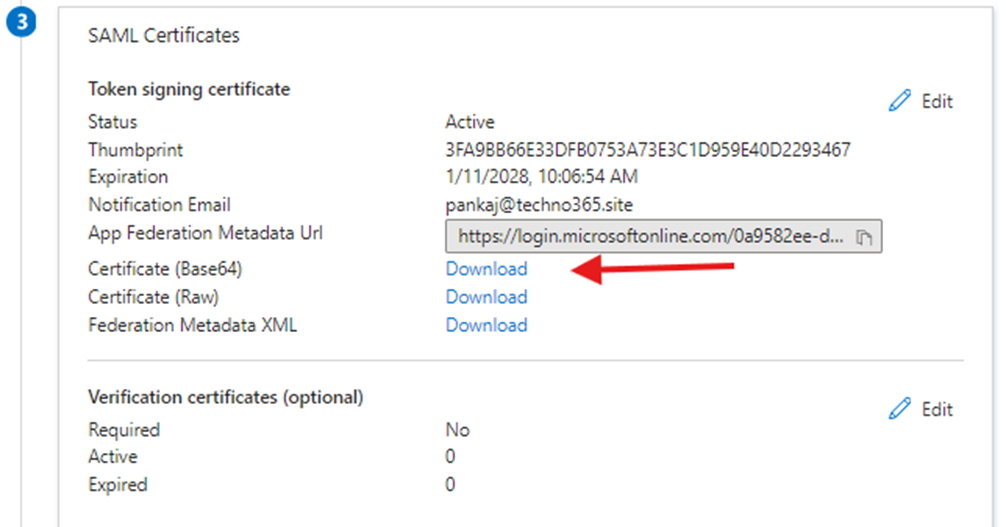
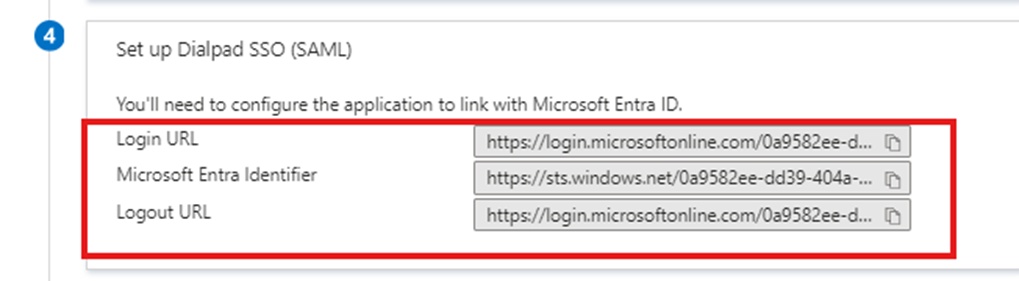
- Note the Login URL and Microsoft Entra Identifier for later use under the Set up Dialpad SSO (SAML).
Step 4: Complete SSO Setup in the Dialpad Admin Portal
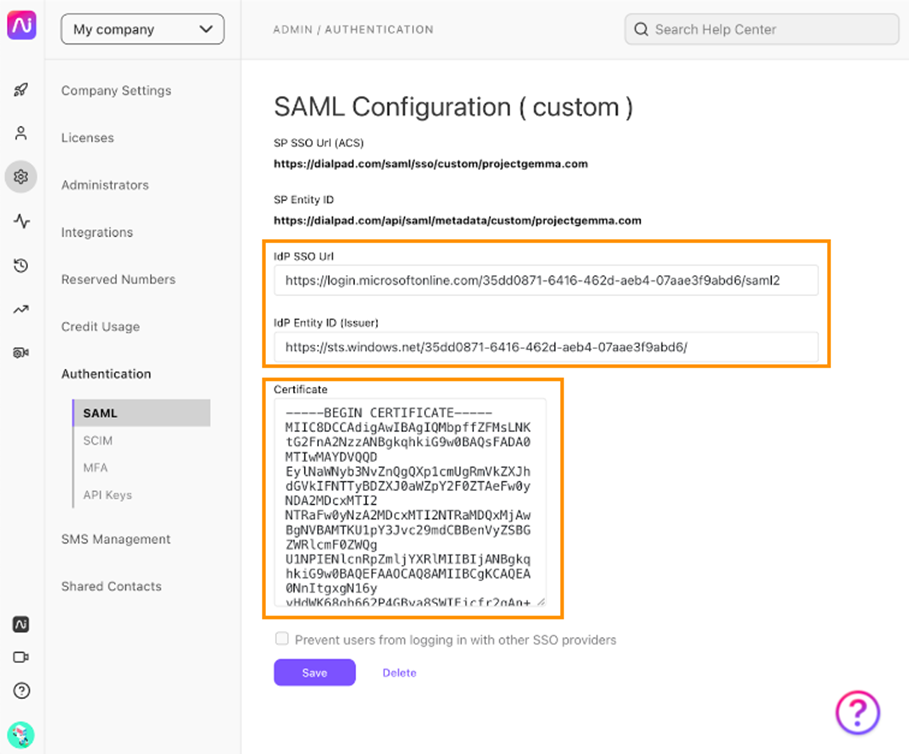
- Add the Login URL and Microsoft Entra Identifier to the Dialpad admin portal.
- Upload the certificate downloaded from Azure AD.
- Save the changes.
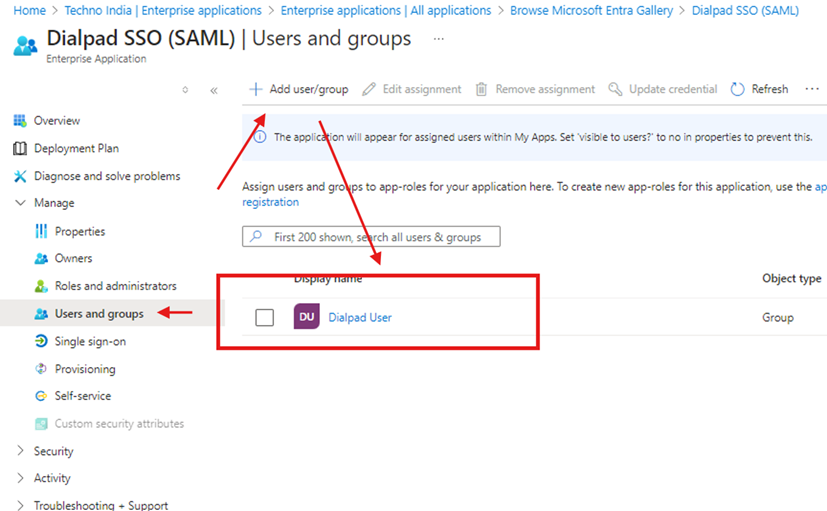
Step 5: Assign Users and Groups in Microsoft Entra ID
- Go to Users and Groups in the Dialpad app in Azure AD.
- Click Add Assignment and assign users or groups to the app.
Testing the SSO Configuration
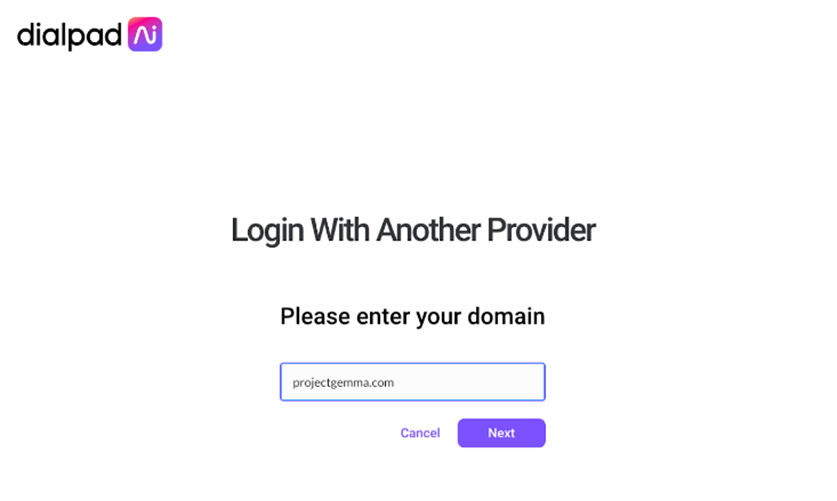
- Log in to Dialpad using Microsoft Entra ID credentials.
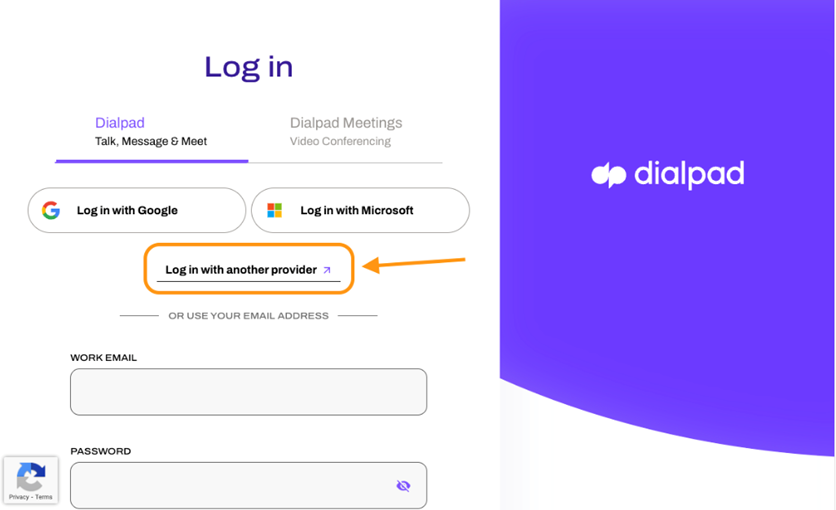
- Confirm successful redirection and authentication.
- Test with multiple users to verify mapping and permissions.
Troubleshooting Common Issues
- Login Failure: Verify Identifier and Reply URL fields in the SAML configuration.
- Attribute Mapping Errors: Ensure user attributes align between Microsoft Entra ID and Dialpad.
- Access Denied: Confirm that users/groups are assigned to the Dialpad app in Microsoft Entra ID.
Best Practices for SSO Integration
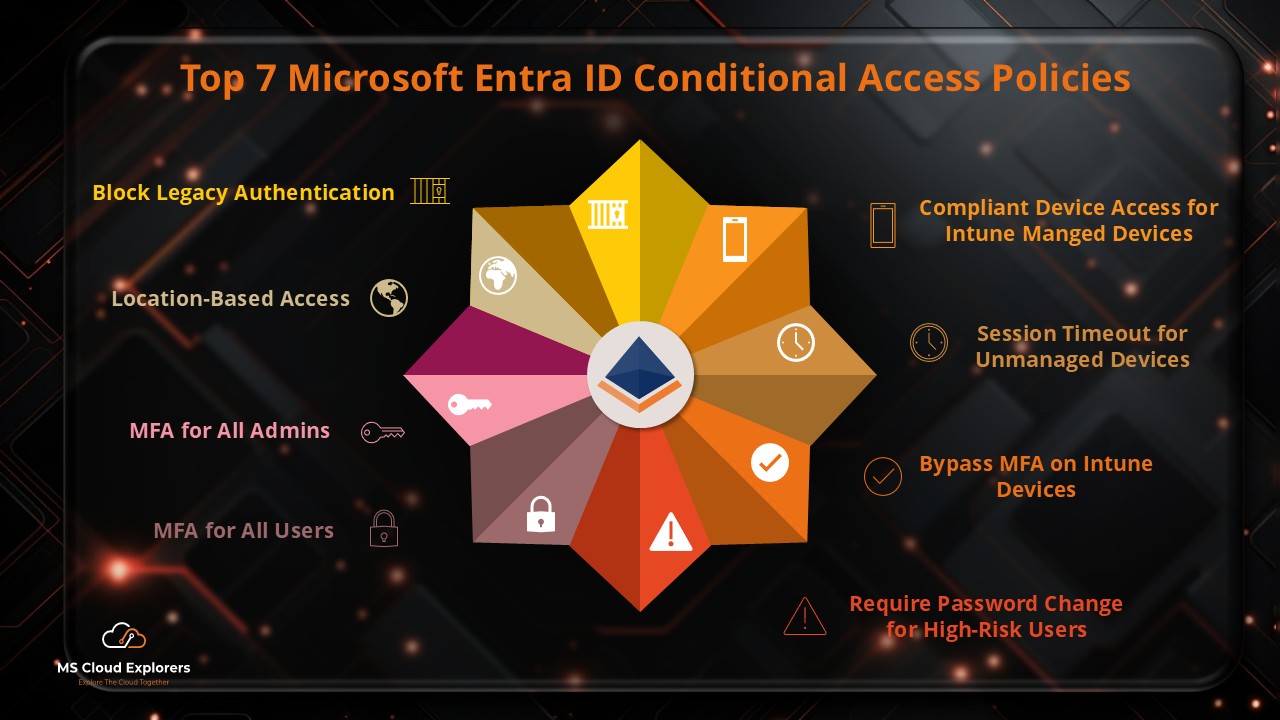
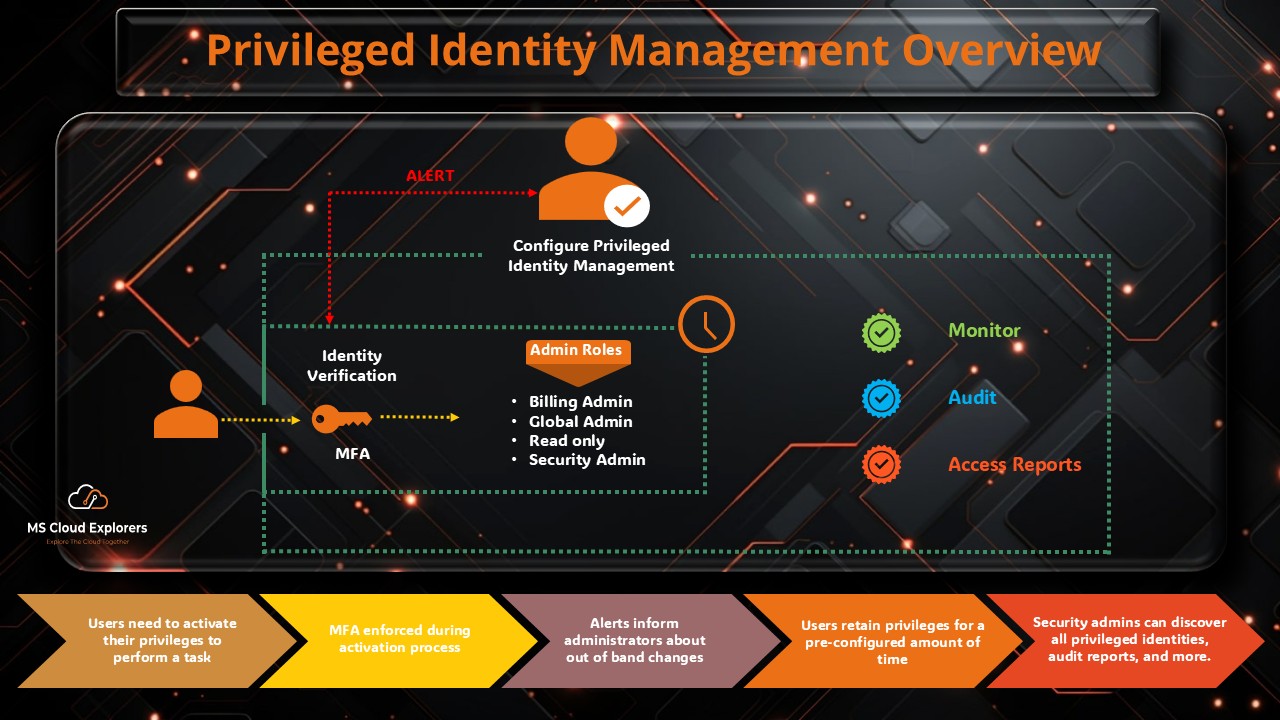
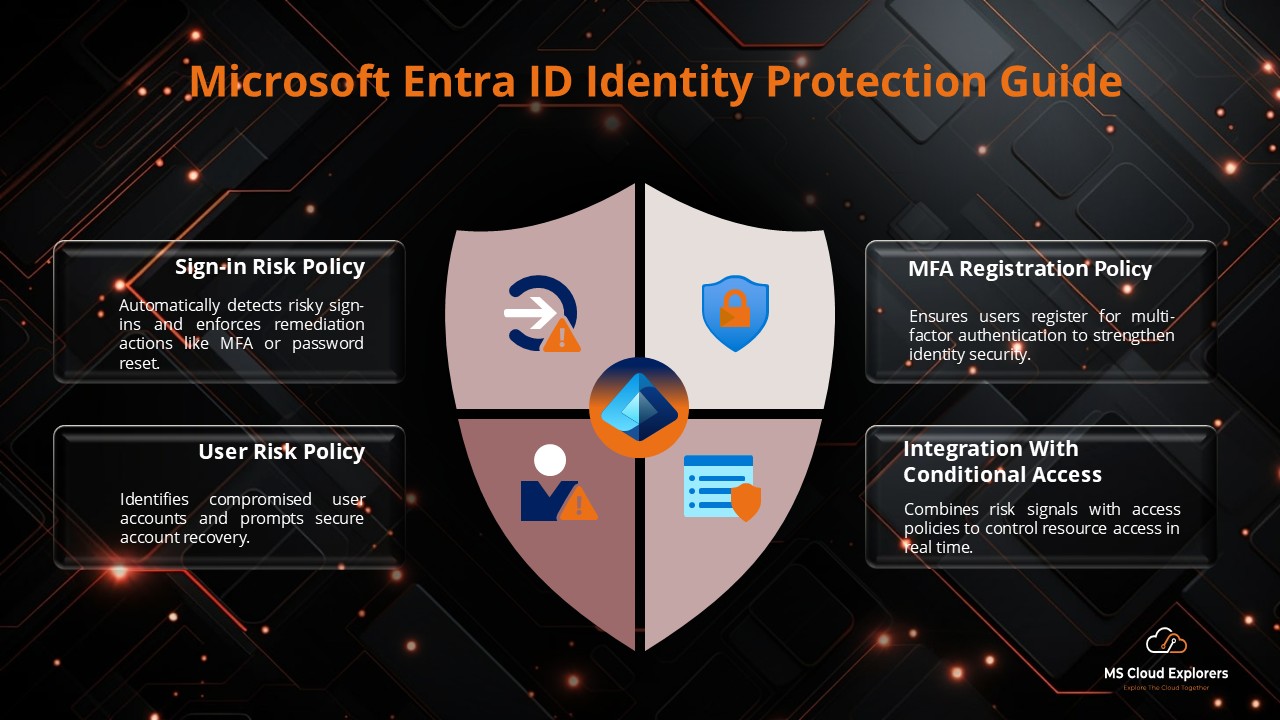
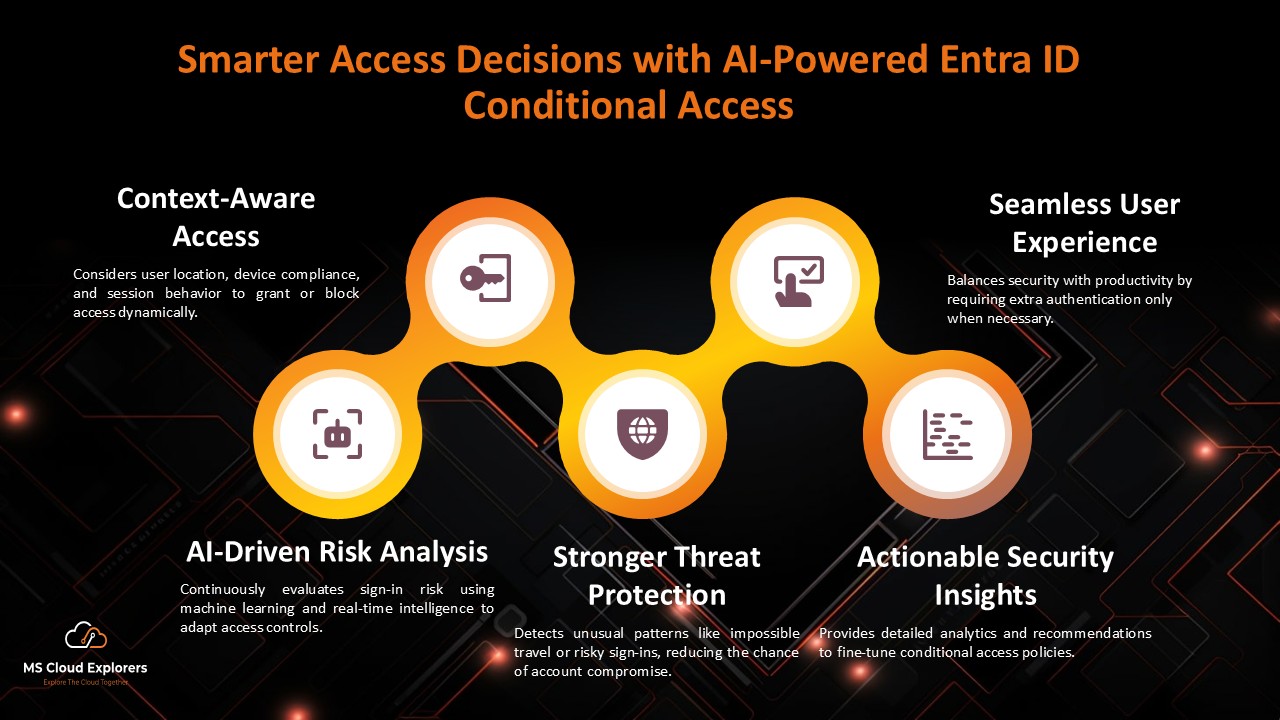
- Use Conditional Access Policies to require MFA for Dialpad access.
- Regularly update SSO metadata to avoid disruptions.
- Monitor Microsoft Entra ID logs for insights and potential issues.
Conclusion
Integrating Dialpad with Microsoft Entra ID using Single Sign-On (SSO) is a smart and effective way to simplify user access while strengthening your organization’s security.
Instead of managing multiple passwords and dealing with frequent login issues, SSO allows users to access Dialpad seamlessly using their existing organizational credentials. This not only improves the user experience but also reduces the burden on IT teams by minimizing password reset requests and access-related support tickets.
By following this step-by-step guide, you can confidently set up Dialpad SSO with Microsoft Entra ID and ensure a secure, efficient, and user-friendly authentication experience.
Related URLs:-
- Step-by-Step Guide to Package and Deploy Dialpad App Using Intune
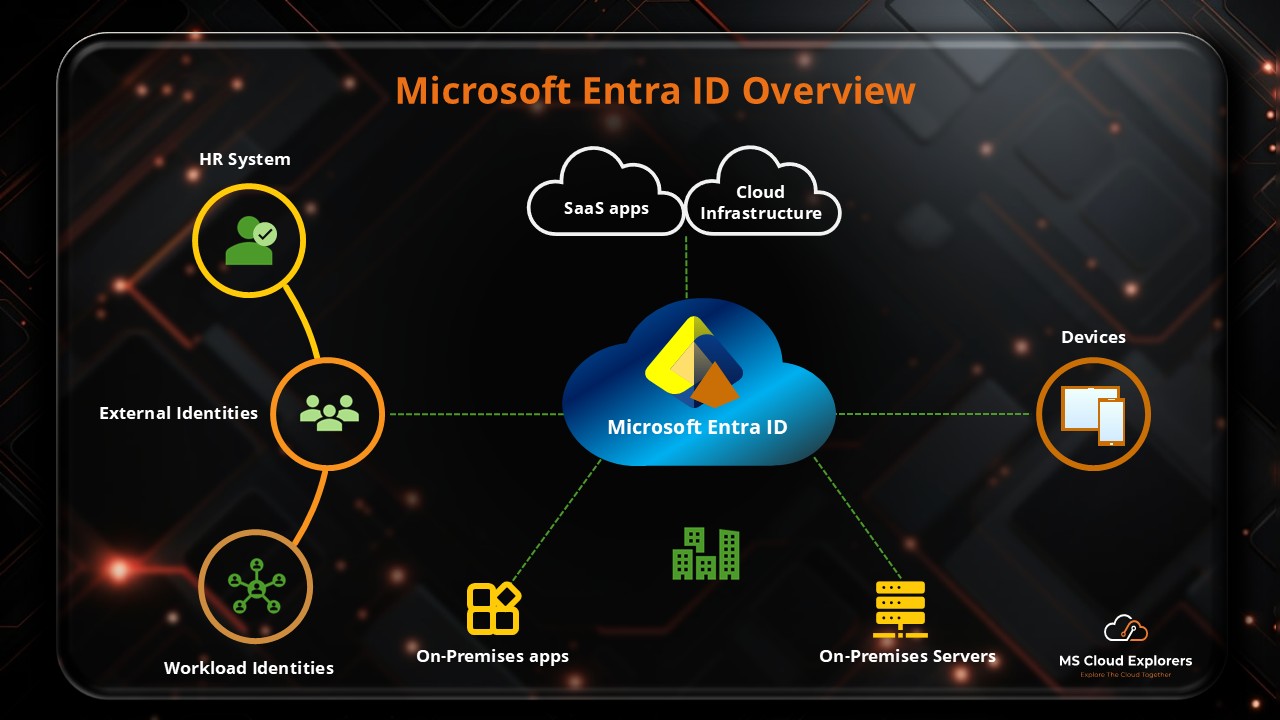
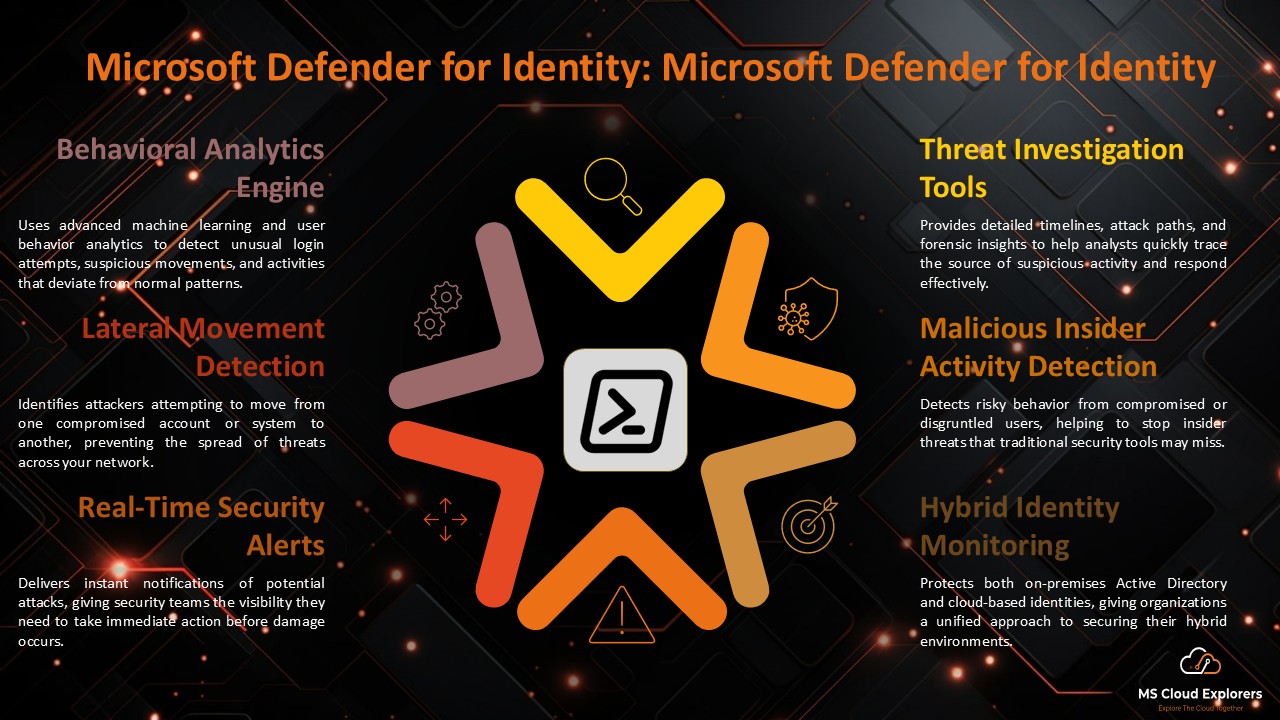
- Microsoft Entra ID: Complete Guide, Features, Security, and Subscriptions
- Microsoft Entra ID Identity Protection: A Complete Guide to Securing Your Digital World
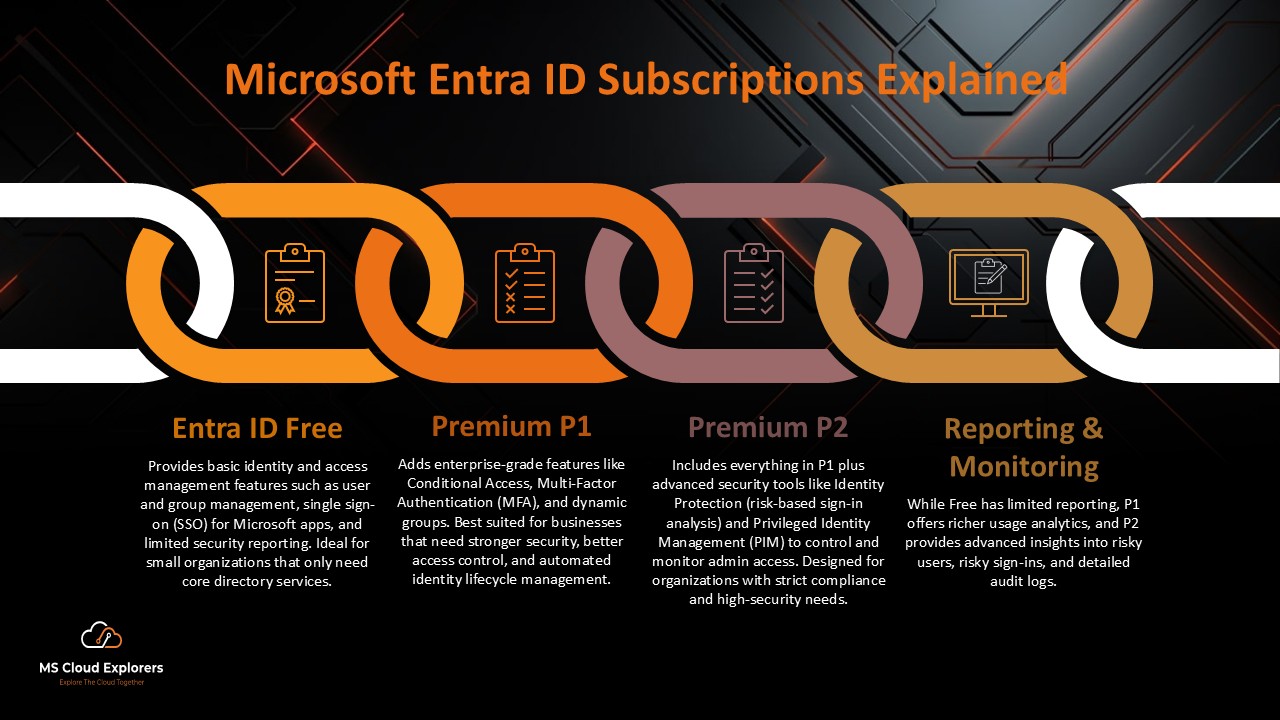
- Azure AD Free vs. Premium P1 & P2: Which Edition Is Right for Your Business?
Enjoyed the article?
We’d love to hear your thoughts—share your comments below!
For more insights, guides, and updates from the Microsoft ecosystem, be sure to subscribe to our newsletter and follow us on LinkedIn. Stay connected and never miss out on the latest tips and news!



Thanks for providing great guide on this. I have completed my SSO for dialpad for my company.
checking if there are auto provision option for new users.
This is great blog, please help me the deploy Dialpad with Intune also
Yes, If you add any of new user in the Dialpad user group, they will automatically will be added in dialpad.
This is exactly what I was looking for—helped me configure group-based access and automatic provisioning effortlessly. One thing I’d love to see in a future update: how to troubleshoot common SAML errors when implementing SSO.
guide is already created, please check out other blogs on Intune and you should able to find the guide what you are looking for.
Excellent suggestion about SAML troubleshooting—great call. We’re working on adding a dedicated troubleshooting section that covers common issues like certificate mismatches, attribute mapping errors, and SSO session failures. It should go live within the next week!
Perfect timing—I was just evaluating whether our Azure AD tier supports automatic provisioning. The article helped clarify prerequisites and SAML‑claim steps. You’ve saved me a lot of troubleshooting!
That’s great to hear! We’re thrilled the timing worked out and that the content saved you some effort. More provisioning-focused content is on the way—stay tuned!